 <-- Racist 1:10:00
<-- Racist 1:10:00- Redhot1960
- 12-27-2020, 01:42 PM
 <-- Racist 1:10:00
<-- Racist 1:10:00- Yssup Rider
- 12-27-2020, 03:40 PM
Angry white women.
Could at least have cast it a little more careflly, don't you think?

AHHAHAAHAHAHAHAHAAAAAAAAAHHHHH HHH
Could at least have cast it a little more careflly, don't you think?

AHHAHAAHAHAHAHAHAAAAAAAAAHHHHH HHH
- EverybodyLovesFangFang
- 12-28-2020, 08:32 AM
Angry white women.White suburban women may have been revolted by Trump's rough edges but they still do not want crime in their neighborhood nor higher taxes.
Could at least have cast it a little more careflly [sic], don't you think?
AHHAHAAHAHAHAHAHAAAAAAAAAHHHHH HHH Originally Posted by Yssup Rider
Chances are, they will not vote for Democrat Senators, but time will tell.
- Yssup Rider
- 12-28-2020, 08:47 AM
Not like they did in November?
Yeah, the Republicans have bent over backwards to earn that vote back.
HAHAHAHAHAHAHAHAHAHA!
Yeah, the Republicans have bent over backwards to earn that vote back.
HAHAHAHAHAHAHAHAHAHA!
- EverybodyLovesFangFang
- 12-28-2020, 12:11 PM
- Redhot1960
- 12-28-2020, 04:18 PM
 <-- Racist 43
<-- Racist 43 "Keln" made this graphic on this video for The Conservative Treehouse. Freedom!
- Yssup Rider
- 12-28-2020, 05:28 PM
- oeb11
- 12-29-2020, 09:18 AM
AS hh wrote- don't vote for 'teh; party of failures!!
- Munchmasterman
- 12-29-2020, 09:48 AM
What a douche-bag!
Clinton?
You've sucked every dick there is!
And now you pretend you want pussy?
You and yours have been crushed. Your posts are increasingly desperate.
trump's supreme court hates you as much as the rest of America does.
You have nothing. Which is more than you deserve.
Clinton?
You've sucked every dick there is!
And now you pretend you want pussy?
You and yours have been crushed. Your posts are increasingly desperate.
trump's supreme court hates you as much as the rest of America does.
You have nothing. Which is more than you deserve.
AS hh wrote- don't vote for 'teh; party of failures!!
Originally Posted by oeb11
- Yssup Rider
- 12-29-2020, 09:59 AM
- Redhot1960
- 12-29-2020, 04:15 PM
 <-- Racist
<-- Racist42
- Redhot1960
- 12-29-2020, 04:30 PM
 <-- Racist
<-- Racistdouche-bag ClintonThey Rigged the Voting Machine Software so Donald Trump Could Never Win.
sucked every dick there is!
Originally Posted by Munchmasterman
Various Resources | 12/29/2020 | Various Resources
Posted on 12/29/2020, 4:36:35 PM by Son House
That's the headline that needs to go out in every news outlet. And those local news
outlets that are following in the media narrative, they should know this too.
Mathematical And Data Analysis links included.
Analysis of 2020 Presidential Election vote count reporting anomalies
https://sites.google.com/view/2020pr...otecounts/home
Index
Vote counting irregularities in visible counts
Trump to Biden Vote Switches
Vote Losses
Spurious Vote Additions
Per precinct vote count and visible vote count mismatches
Exhibits Included
Conclusion
As demonstrated above there is evidence beyond reasonable doubt of illegal
vote count manipulation by vote counting/reporting software used in
multiple states, indicative of systemic issues in this election. The data
shows that upwards of a million votes were thrown out or switched in
Pennsylvania and several thousand in the other states.
Also, as shown in the previous section there is smoking gun evidence of
stealing write-in votes and infusion of fake absentee vote counts by Scytl
and Dominion reporting software. A full audit and hand recount of all legal
ballots cast in the affected states should be done, to ensure that legal
voters are not disenfranchised.
Remember this, go read Page 1, points 5,6,7, and 8, I cant copy/paste it.
Submitted sworn affidavit;
https://www.courtlistener.com/recap/...92717.9.13.pdf
112. During the 2014 elections in it was the modems that gave access to the
systems where the commitment keys were deleted.
Backtrack just a little;
89. Under the guise of Crisis support the US Federal Tax Payers funded the
deployment of the election software and machines in signing on with Scytl.
Must see Exhibit for answer in Page 27
US Crisis Support Package for Ukraine;
90.Exhibit 13
91. Right before the -elections it was alleged that CyberBerkuta pro-
Russia groupinfiltrated -central election computers and deleted key files.
These actions supposedly rendered the vote-tallying system inoperable.
92. In fact, the KEY FILES were the Commitment keys to allow Scytl to tally
the votes rather than the election machines. The group had disclosed emails
and other documents proving that their election was rigged and that they
tried to avoid a fixed election.
93. The elections were held on May 25, 2014 but in the early AM hours the
election results were BLOCKED and the final tally was DELAYED flipping the
election in favor of -.
94. The claim was that there was a DDoS attack by Russians when in actual
fact it was a mitigation of the algorithm to inject block votes as we
observed was done for Joe Biden because the KEYS were unable to be deployed.
In the case of -, the trap-door key was altered/deleted/ rendered ineffective.
In the case of the US elections, representatives of Dominion/ ES&S/
Smartmatic/ Hart Inter-civic would have to manually deploy them since if the
entry points into the systems seemed to have failed
Video 2hr 20m The Mathematics Explained, Several Links Included
The Wheel Of Michigan! Net total over 280,000 votes stolen from Trump!
https://thedonald.win/p/11RNtTOMxZ/s...d-the-wheel-o/
Video here
https://rumble.com/vc7wxd-smoking-gu...votes-sto.html
Video here
https://www.bitchute.com/video/0OnAWJSEZGWa/
Oakland County: Trump suffers a net loss of 112,044 votes. Kent County: Trump
suffers a net loss of 44,053 vote (in agreement with Dr. Shiva).
All remaining counties in the analysis: Trump suffers a net loss of 34,518 votes.
Remember this, go read Page 1, points 2, and 3, COTS (Commercial OffThe-Shelf)
Submitted sworn affidavit;
https://www.courtlistener.com/recap/...92717.9.13.pdf
99. ...COTS are an avenue that hackers and bad actors seek to penetrate in order
to control operations. Their software updates are the reason vulnerabilities to
foreign interference in all operations exist.
108. The significance of VSTLs being accredited and examining the HARDWARE is key.
COTS software updates are the avenues of entry.
109. As per DOMINIONS own petition, the modems they use are COTS therefore
failure to have an accredited VSTL examine the hardware for points of entry by
their software is key.
111. For example and update of Verizon USB Modem Pantech undergoes multiple
software updates a year for its hardware. That is most likely the point of entry
into the systems.
112. During the 2014 elections in it was the modems that gave access to the
systems where the commitment keys were deleted.
Voting System Test Laboratories (VSTL)
https://www.eac.gov/voting-equipment...oratories-vstl
Section 231(b) of the Help America Vote Act (HAVA) of 2002 (42 U.S.C. §15371(b))
requires that the EAC provide for the accreditation and revocation of
accreditation of independent, non-federal laboratories qualified to test voting
systems to Federal standards.
Video, seem to be in chronological order from Nov 3.
Timestamps in reverse, about 1 hour 30 minutes
2020 Election Investigative Report
https://www.youmaker.com/video/60bb9...0-420b9621cb57
-1:26:40m Michigan and Wisconsin 4am and 6am
-1:24:00m Similar Anomalies Edison Research
-1:22:30m Presidential vs Senate candidate
-1:20:00m Mail-in ballots whistle-blower didnt recant
-1:17:30m Video forwarded, other poll worker list to not let in
-1:14:00m Sent 17 Mail-in ballots, many other observations
-1:11:11m Set up Data Analyst across 6 states Georgia detailed, absentee ballots too
-1:07:40m Data Analyst Wisconsin, Arizona
-1:06:55m Video from State Farm Arena, Fulton County Georgia
More complete index here;
https://freerepublic.com/focus/chat/...page=7559#7559
Antrim County Forensic Report Shows Manipulation of Votes
https://uncoverdc.com/2020/12/14/ant...tion-of-votes/
Likewise, they found that all the server security logs from 11:03 p.m. on Nov. 4, are also
missing. Security logs provide critical information about audit trail, forensics, and for
detecting advanced persistent threats and outside attacks, especially on systems with outdated
system files.
Additionally, the report says that on Nov. 21, 2020, an unauthorized user unsuccessfully
attempted to zero out election results, demonstrating further evidence of tampering with data.
The logs also show that Dominion ImageCast Precinct Cards were programmed with new ballot
programming on 10/23/2020 and then again after the election on 11/05/2020.
The report states that the only reason the software would be altered after an election would be
to hide fraud and/or to correct errors that would decertify the election. The team concludes
that software changes during an election, a violation of election law, cannot be explained by
human error, but is clear evidence of software-generated movement of votes. Therefore, the
report concludes that the claims made on the Secretary of State website are false.
More on that Audit;
Antrim County Forensic Report Shows Manipulation of Votes
https://freerepublic.com/focus/chat/...page=1358#1358
The allowable election error rate established by the Federal Election Commission
guidelines is of 1 in 250,000 ballots (.0008 percent). The team, however, observed
an error rate of 68.05 percent.
https://freerepublic.com/focus/chat/...page=1366#1366
Another stunning revelation was the fact that adjudication logs were present in the system from
other years but not from 2020.
The lack of records prevents any form of audit accountability, and their conspicuous absence is
extremely suspicious since the files exist for previous years using the same software. Removal of
these files violates state law and prevents a meaningful audit, even if the Secretary wanted to
conduct an audit. We must conclude that the 2020 election cycle records have been manually removed.
Video Here, 2:15m;
Have 2020 Ballots and Images Audited in Select States
https://www.thegatewaypundit.com/202...van-pulitizer/
Almost a 94% Adjudication rate.
28:20m, Server to usher elections in Ukraine
Video Report
https://twitter.com/Millie__Weaver/s...92309543702528
First a definition, go see Pages 23 - 28, Then all of Page 34
Submitted sworn affidavit;
https://www.courtlistener.com/recap/...92717.9.13.pdf
55. ...In other words, Scytl or anyone that knows the commitment
parameter scan take all the votes and give them to any one they want. If they have
a total of 1000 votes an algorithm can distribute them among all races as it deems
necessary to achieve the goals it wants. (Case Study: Estonia)
137. That there was Foreign interference, complicit behavior by the previous
administrations from 1999 up until today to hinder the voice of the people and US
persons knowingly and willingly colluding with foreign powers to steer our 2020
elections that can be named in a classified setting.
Case about weighted race computer algorithms were used, Dr Shiva
10:55 PM · Dec 25, 2020
Filed Amended Complaint for DECERTIFICATION of 2020 MA U.S. Senate race
https://twitter.com/va_shiva/status/1342695556540456960
Dec 26, 2020
Heres the PDF to the Amended Complaint
https://vashiva.com/wp-content/uploa...-Complaint.pdf
Mathematical evidence demonstrating that computer algorithms for weighting votes were
used in the 2020 U.S. Senate Republican primary to debase dilute the vote of both Dr. Shiva
and every person who voted for him such that they were turned into 2/3rds of a person.
https://twitter.com/va_shiva/status/1342888491215187973
Which politician in the US has boldly called out Election Fraud? That question
provides you a litmus test of who is in the Club - or wants to be in it -, and who is
not in the Club - and wants no part of it. Real science is all about observation.
Truth reveals itself - always.
Given a definition also go see Pages 23 - 28, Then go see all of Page 34
Submitted sworn affidavit;
https://www.courtlistener.com/recap/...92717.9.13.pdf
55. ...In other words, Scytl or anyone that knows the commitment parameter scan
take all the votes and give them to any one they want. If they have a total of 1000
votes an algorithm can distribute them among all races as it deems necessary to
achieve the goals it wants. (Case Study: Estonia)
64. In many circumstances, manipulation of the algorithm is NOT possible in an
undetectable fashion. This is because it is one point heavy. Observing the
elections in 2020 confirm the deployment of an algorithm due to the BEHAVIOR which
is indicative of an algorithm in play that had no pivoting parameters applied.
Then go see all of;
Page 34
137. That there was Foreign interference, complicit behavior by the previous
administrations from 1999 up until today to hinder the voice of the people and US
persons knowingly and willingly colluding with foreign powers to steer our 2020
elections that can be named in a classified setting.
Video 53s, on Antrim county.
Forensic AUDIT in Savannah GA, tabulation machines;
https://twitter.com/Grhm_i/status/1342649524469309442
Already knew there was a huge over-seas problem.
- Redhot1960
- 12-29-2020, 05:16 PM
Another Racist article  https://creativedestructionmedia.com...at-since-2003/
https://creativedestructionmedia.com...at-since-2003/
Cracking Dominions Source Code A National Security Threat Since 2003
by George EliasonDecember 29, 2020116958
Did Donald Trump Catch Dominion And Smartmatic US Election Racketeering?
Dominion ImageCast precinct count optical ballot scanner
Image by Douglas W. Jones
With the Georgia runoff election in full swing, this article will show why the ballot results should be ash-canned even before the final tallies are in both Georgia and Pennsylvania adhere to the federal standard for elections and because Dominion uses modems, the election provider itself is not certifiable.
Pennsylvania state certification requires that voting systems be evaluated by a federally recognized independent testing authority, or voting system test laboratory (VSTL), and certified by the U.S. Election Assistance Commission (EAC) according to federal voting system standards.
Once you add that modem, you are de-certifying it, Kevin Skoglund, senior technical advisor at the National Election Defense Coalition said. It is no longer federally certified. And I dont know that all these jurisdictions are aware of that because ES&S is advertising otherwise. The three largest voting manufacturing companies Election Systems &Software, Dominion Voting Systems and Hart InterCivic have acknowledged they all put modems in some of their tabulators and scanners.-NBC
What youre going to find is the current Dominion and ES&S voting systems were designed over 22 years ago to allow and promote every type of voter fraud imaginable and the same two conspirators have been safeguarding and selling these broken systems the entire time.
From 1997 to 2003 Bob Urosevich and Barry Herron developed the art of electronic vote manipulation to such a degree; you didnt need to hack the system to change the election results. Below is the chain of custody for the software and source code that made this possible.
The key takeaway is simple. Although whats described below is from Diebold Election Systems, Dominion bought Diebold and this system for use. This the backbone of Dominion Voting Systems today and it gives a clear line of sight into the otherwise opaque world of election fraud in 2020.
In 2003, a research journalist named Bev Harris opened up the world of Diebold Election Systems. When Dominion Voting Systems got off the ground and became a player it was because of the purchase of Diebold properties including systems, source code, and software.
What she found was Diebold had a no-login needed website that was a detailed manual of how to hack the election systems Diebold was servicing across the US. If you didnt like the election tallies, it was a simple matter of replacing the file with one that reflected the results you wanted on this FTP site.
CDMedia is being de-platformed and obviously too effective! We need your support to put more reporters in the field! Help us here!
According to Harris, the site was set up for election workers and technicians and included hardware and software specifications, election results files, the vote-counting program itself, and replacement files for Diebolds GEMS vote-counting system and for the Windows software underlying the system.
The contents of these files amounted to a virtual handbook for vote-tampering: They contained diagrams of remote communications setups, passwords, encryption keys, source code, user manuals, testing protocols, and simulators, as well as files loaded with votes and voting machine software.
Diebold Elections Systems AccuVote systems use software called GEMS, and this system is used in 37 states. The voting system works like this:
Voters vote at the precinct, running their ballot through an optical scan, or entering their vote on a touch screen.
After the polls close, poll workers transmit the votes that have been accumulated to the county office. They do this by modem.
At the county office, there is a host computer with a program on it called GEMS. GEMS receives the incoming votes and stores them in a vote ledger. But in the files we examined, which were created by Diebold employees and/or county officials, we learned that the Diebold program used another set of books with a copy of what is in vote ledger 1. And at the same time, it made yet a third vote ledger with another copy.
Apparently, the Elections Supervisor never sees these three sets of books. All she sees is the reports she can run: Election summary (totals, county wide) or a detail report (totals for each precinct). She has no way of knowing that her GEMS program is using multiple sets of books, because the GEMS interface draws its data from an Access database, which is hidden. And here is what is quite odd: On the programs we tested, the Election summary (totals, county wide) come from the vote ledger 2 instead of vote ledger 1, and ledger 2 can be altered so it may or may not match ledger 1.
Now, think of it like this: You want the report to add up only the actual votes. But, unbeknownst to the election supervisor, votes can be added and subtracted from vote ledger 2. Official reports come from vote ledger 2, which has been disengaged from vote ledger 1. If one asks for a detailed report for some precincts, though, the report comes from vote ledger 1. Therefore, if you keep the correct votes in vote ledger 1, a spot check of detailed precincts (even if you compare voter-verified paper ballots) will always be correct.
Auditing
Again from Bev Harris provided all this information on a share-as-widely-as-possible basis. The audit trail is what is supposed to guarantee election security. Harris went to the same Diebold/Dominion website and downloaded a GEMS (General Election Management System) audit report.
Note that a user by the name of Evildoer was added. Evildoer performed various functions, including running reports to check his vote-rigging work, but only some of his activities showed up on the audit log.
It was a simple matter to eliminate Evildoer. First, we opened the election database in Access, where we opened the audit table: Then, we deleted all the references to Evildoer and, because we noticed that the audit log never noticed when the admin closed the GEMS program before, we tidily added an entry for that.
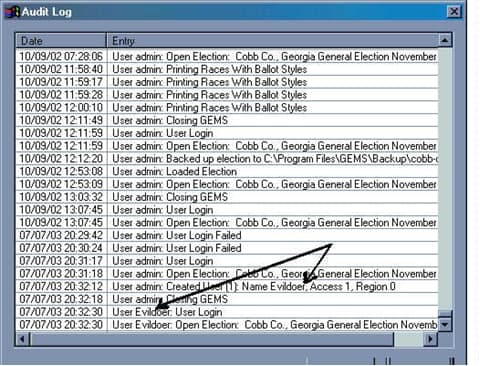
Access encourages those who create audit logs to use auto-numbering so that every logged entry has an uneditable log number. Then, if one deletes audit entries, a gap in the numbering sequence will appear. However, we found that this feature was disabled, allowing us to write in our own log numbers. We were able to add and delete from the audit without leaving a trace. Going back into GEMS, we ran another audit log to see if Evildoer had been purged:
As you can see, the audit log appears pristine.
In fact, when using Access to adjust the vote tallies we found that tampering never made it to the audit log at all. Bev Harris
An election (after the fact) using the real files on the real system was changed for research purposes with no elaborate hacking necessary.
The Dominion software and source code was originally developed by a company called Premier Election Solutions. The founder was Bob Urosevich.
In 1997 Global Election Systems acquired Premier. The company representatives were Bob Urosevich and Barry Herron
In 2001, Diebold purchased Global. The company representatives were Bob Urosevich and Barry Herron.
In 2009, Diebold Sells U.S. Elections Systems Business to ES&S. The company representatives were Bob Urosevich and Barry Herron
In September 2009, ES&S acquired Premier, without any objections from the DOJ. But in March 2010, the DOJ forced ES&S to sell Premiers assets to Dominion. ES&S was also forced to license to Dominion some of its software for free.
Dominion announced the acquisition of the Diebold (formerly Premier) products on May 19, 2010
Dominion Voting Systems purchased the primary assets of Premier, including all intellectual property, software, firmware, and hardware for Premiers current and legacy optical scan, central scan, and touch screen voting systems, and all versions of the GEMS election management system from ES&S.
Barry Herron is the Southeast regional sales manager for Dominion Voting Systems as well as being their lobbyist.
Barry Herron is Director of sales for INTERNATIONAL LOTTERY AND TOTALIZATOR, INC.
Barry Herron is the sales manager for Unisyn Voting. Unisyn, an HK registered company wholly owned by UNISYN VOTING SOLUTIONS (A DIVISION OF INTERNATIONAL LOTTERY AND TOTALIZATOR, INC) a division of Berjaya Lottery Management (h.k.) Ltd, a division of Yong Hong Group Co., Ltd., referred to Wing Hung Kai Group ( English: Wing Hung Kee Holdings Limiteds, HKEx except when licensing 0288.HK), founded in 1971, formerly known as Wing Hung Kai Properties Limited referred to as Wing-hong Kee Property ( English: Wing Hung Kee Investment Company, Limited ). Listed on the main board of the Hong Kong Stock Exchange in 1973. In 1994, the Malaysian consortium Berjaya Group ( Berjaya Group ) acquisition, changed its name to succeed Holdings (Hong Kong) Limited.
Unisyn is a wholly-owned private corporation headquartered in Malaysia but registered in Hong Kong, China.
INTERNATIONAL LOTTERY AND TOTALIZATOR, INC is the worlds largest manufacturer of voting machine equipment.
Does Unisyn manufacture Dominion Voting Solution machines? I dont have the answer to that but Unisyns Barry Herron is Dominions lobbyist for GA.
Along with Bob Urosevichs ES&S, Unisyn is also one of the voting systems companies certifying the 2020 US election was the safest in history.
How important is this information? If attorneys Rudy Guliani and Sydney Powell dont have this information yet, it will be vital in court to show the voting machine source code and system was known to be threats to national security in its previous use.
Throughout the rest of this article, Ill be referring to background The Case of the Diebold FTP Site Part of the Voting and Elections web pages by Douglas W. Jones Head of THE UNIVERSITY OF IOWA Department of Computer Science. The reference will be (DWJ). His study which refers to The Johns Hopkins Study On Voting Systems (Hopkins) as well as the SAIC (Science Applications International Corp). These three reports led to the decertification of the previous iteration of Dominions source code and software in various states and Dr. Jones has testified before Congress on these specific issues.
Ill also be referring to the NBC article (NBC), Online and vulnerable: Experts find nearly three dozen U.S. voting systems connected to internet which shows the problems the same voter software and source code used by Global Elections over 20 years ago is why Dominion Voting Systems/Diebold and ES&S/Diebold are still a national security threat today the same way they were labeled as such 17 years ago.
Lastly, How New Voting Machines Could Hack Our Democracy Jennifer Cohn for the New York Review of Books (NYRB) shows the updated methodology combined with Dominions source code makes election fraud easy. Comparing this to the Hopkins study or the paper by (DWG) its clear the level of threat election security is facing today.
At every waypoint in the election cycle from certification, planning, voting, absentee and mail-in votes, county reporting on the GEMS (General Election Management Systems), this system provides the means to monitor and change votes in real-time and even during the ballot reporting at the county level.
Throughout its history, whenever Diebold/Dominions source code, software, and method were inspected, it was moved under a new corporate logo.
How secure are the 2020 elections?
Cracking Dominions Source Code - A National Security Threat Since 2003
Using Modems for federal elections decertifies voting machines.
The state of Michigan is currently grappling with this issue. Since the 2016 election, Michigan authorized $82 million dollars to upgrade its election systems. Some of that money was spent on tabulators with wireless modems. But now, some state officials worry that the machines may pose a security risk and are pushing to have the modems removed.(NBC)
Some of the companies, agencies, groups, and people certifying the 2020 election as the safest in history represent a whos who of people to investigate for 2020 election fraud. If one voting system company is looked at under a microscope, more of them will fall soon thereafter.
For Georgia, this means the broken Diebold system Herron replaced with new Dominion machines is the same made to be hacked system Georgia already had with a few new add-ons.
LAN and hard lines
Because hacking into the systems is easy they way Diebold/Dominion set it up, according to (DWG)s report even the use of LAN and hard lines pose a significant security problem.
Allegation #53 (p. 16):
Physical access to the voting results may not even be necessary to acquire the voting records if they are transmitted across the Internet.
Diebold Response:
Results are not transmitted over the Internet.
My Added Comment:
But we know that result transmission uses telephone, PPP, and a username and password, from Page 14 of the Hopkins report, quoted in Allegation #40. Therefore, it is quite possible that election central will have a LAN connection using Internet protocol, perhaps used to connect a modem bank with a single PC. This LAN may not be as vulnerable as the public Internet, but it is vulnerable to packet snooping and several other attacks, and must therefore be carefully secured. Furthermore, if an adversary can dial into the PPP host and await connections, Trojan horse applications on the voting system could communicate with the adversary using PPP without talking to the GEMS system at all. (DWG)
In its previous iteration under the Diebold logo, access to GEMS was already provided. Using a latent Trojan or latent dynamic code that isnt detectable during certification or is added later and goes live during the election isnt just possible with this system. Every door for it happening has been left open for over 22 years of election cycles.
Diebold (now Dominion) made public assurances that GEMS servers were/are not connected to networks despite the fact that some were. If GEMS has a pool of modems it is connected to the telephone system and security depends on how the modems are managed and who is managing them. Telephone networks are considered part of the internet. A GEMS server could be dialed and corrupt data directly. The modem bank can be tunneled through to gain access to the polling places and corrupt election machines directly. (DWG)
That fact alone along with Dominion Voting Systems specifically being the owner of this system is enough to decertify not just the elections Dominion contracted for, but the equipment itself, already long considered a threat to election security.
Intrusion into the General Election Management System (GEMS)
From its inception this election system used 3rd party add-ons. This includes Microsoft Windows OS and Microsoft Office software which depending on the definition used for can be loaded with other COTS (commercial off the shelf 3rd party software).
The problem found with Microsoft components (DWG) is the use of dynamic coding which can be used to change ballot results. From the beginning (1997), Bob Urosevich and Barry Herron insisted this was not subject to a source code audit.
The same Microsoft ACCESS program is shown above to swiftly and undetectably change the audit trail and results is what Diebold/ES&S and Diebold/Dominion demand protection for.
When Diebold (using Dominions current source code) was audited by Metamor for the FEC/NASED, they found the security of GEMS and the integrity of the audit trails were compromised because Microsoft Access can easily change that audit trail.
Diebold (now Dominion) convinced Metamor this wasnt a problem for them because it was up to the customer to secure the election. In other words, they provided the means, training, and support for the crime, but cannot be held liable themselves.
According to (DWGs report) this was despite the fact that Diebold (now Dominion) was aware that this security was being routinely breached: Jane (I think it was Jane) did some fancy footwork on the .mdb file in Gaston [county Florida?] recently, I know our dealers do it. King County is famous for it. Thats why weve never put a password on the file before. [See BlackBoxVoting on Diebolds Internal Memos or Alteration of Audit Log Access.]
While this is damning, it only gets worse. After Diebolds source code was found on their website and examined, the code for the GEMS system used to manage elections and the Accutouch terminal was found. What became clear to (DWG) is the same code errors he pointed out half a decade earlier to Bob Urosevich and Barry Herron at Global Elections followed them to Diebold and was still in use.
This one point made Dr. Jones call for HYPERLINK http://avirubin.com/vote.pdf the decertification of the Diebold (Dominion) system directly after reading the John Hopkins University report.
Mail-in votes
In the (DWJ) report Diebolds (now Dominions) assertion that security loopholes in their voting system is of no importance because customer safeguards prevent exposure.
But, despite supervision in a San Louis Obispo County election, the GEMS system used to accumulate absentee and mail-in ballots were connected to the Diebold FTP site live and the tally of votes was noted midway through the election. For this to be posted on GEMS is normal for any election. How did Diebold comes into possession of this data and post it on their website?
Sneakernet
Before the internet existed, sneakernet was the way hacking was done by loading floppy discs or smartcards into the victims computer and adding malicious code or software.
Weve all seen the videos of thumb drives handed off during the 2020 election. The fact they werent secured should have decertified the results. Smartcards and thumb drives were noted in (DWG)s report as a major concern. In 2003, smartcards provided the interface for concern but these machines were not protected against inconspicuous devices like USB flash drives.
The locks on the machines themselves were noted to be so cheap it took no longer than 3 seconds to go past them. Gaining access took a team testing Diebold security 3 guesses to get the password and because Diebold (Dominion) uses the same login system-wide only one password gained supervisor credentials for every machine.
When Diebold/Dominions source code was read the researchers discovered a class of Security Key Cards that could be used to change default passwords.
Voting Machines
If it were the case that Diebolds machinery offered the possibility of a real audit of an election, in the same way that corporate accounting systems are supposed to be auditable, partisan bias on the part of the vendor would not be a problem, but this is not the case with direct-recording voting machines such as the Diebold AccuVote TS. Democrats want election machine firm thrown out, in the Port Clinton News Herald, August 27, 2003 and Voting machine controversy, in the Cleveland Plain Dealer, August 28.](DWG)
Universal Ballot Marking (BMDs)
According to Jennifer Cohns article on December 17, 2019 (NYRB), Universal use Ballot Marking Devices or BMDs function as electronic pens, mark your selections on paper on your behalf. Although vendors, election officials, and others often refer to this paper as a paper ballot, it differs from a traditional hand-marked paper ballot in that it is marked by a machine, which can be hacked without detection in a manual recount or audit. These pricey and unnecessary systems are sold by opaquely financed vendors who use donations and other gifts to entice election officials to buy them.
These scholars warn that even a robust manual audit, known as a Risk Limiting Audit, cannot detect whether a BMD-marked paper ballot has been hacked. BMDs instead put the burden on voters themselves to detect whether such ballots include fraudulent or erroneous machine marks or omissionseven though studies already show that many voters wont notice.
Andrew Appel, an election security expert at Princeton University, said Georgia currently has the least-secure voting machines now of any state and is right to replace them.
But he said the touchscreen ballot-marking devices and optical scanners of the new system are easily hackable. And the system relies on voters to check their own paper ballots when research shows they do a poor job of it.
Printed-out ballots will include the text of voters choices, but scanning machines will read computerized bar codes to count ballots.-AJC
This means the only real audit trail existing today is in the hands of voters when they leave the polling station. The BMD ballot they cast is unreadable barcode. Their ballot can be changed at every point along the way at the voting machine to the GEMS system.
Patches and new software
The ability to install patches or new software that wasnt certified has many risks, including the introduction of new bugs and more opportunities for tampering. It is even more risky if different patches can be installed at the last minute in particular jurisdictions, says David Dill, professor of computer science at Stanford University.
This opens the possibility of customized tampering by people who know exactly which races they want to affect, or bugs that are even less likely to be caught because they only occur in a small number of locations, says Dill. Of course, even if the certified code is frozen, it is easy to think of ways that undetectable back-doors could be installed in the software so that someone at the election site could choose the winner of the election. -Bev Harris
SAIC Conclusions on Dominions source code
The final paragraph of the executive summary of the SAIC report on the Diebold (now Dominion) system is pretty damning. The system is made to compromise. At the time six years had passed from the time the routes of compromise were discovered and Diebolds system, now owned by Dominion is the same.
The system, as implemented in policy, procedure, and technology, is at high risk of compromise. Application of the listed mitigations will reduce the risk to the system. Any computerized voting system implemented using the present set of policies and procedures would require these same mitigations. [Page V, final paragraph.]
See Risk Assessment Report: Diebold Accuvote-TS Voting System and Processes, SAIC-6099-2003-261, Sept 2, 2003]
Furthermore, since SAIC examined the current certified version of the code, the version number of which was redacted in the body of the text but exposed in Appendix D as 4.3.1.5, this seriously damages Diebolds claims that the flaws reported in the Hopkins study were in old code that is not used in real elections.- (DWG)
With an over 20 year history of providing every means of election fraud possible, training people how to do it, making sure elections are hackable, can Dominion or ES&S claim innocence in 2020?
These election vendors have a history thats mocked in Congress about the bribes they payout to the National Association of Secretaries of State (NASS) and other concerned parties.
Because the 2020 election season was Federal, every machine in every county that was hooked up to a modem was decertified for a federal election. In fact, the argument as shown above can be made for every system connected to any form of telephone systems as a backdoor to the internet and hackers.
Every state using the Dominion system ran decertified elections. The states elected to ignore federal election standards.
Can states that did not meet federal rules for elections after adding them into their own election certification requirements be considered legitimate participants in the 2020 election by choosing to ignore their own election standards?
The answer is no.
 https://creativedestructionmedia.com...at-since-2003/
https://creativedestructionmedia.com...at-since-2003/Cracking Dominions Source Code A National Security Threat Since 2003
by George EliasonDecember 29, 2020116958
Did Donald Trump Catch Dominion And Smartmatic US Election Racketeering?
Dominion ImageCast precinct count optical ballot scanner
Image by Douglas W. Jones
With the Georgia runoff election in full swing, this article will show why the ballot results should be ash-canned even before the final tallies are in both Georgia and Pennsylvania adhere to the federal standard for elections and because Dominion uses modems, the election provider itself is not certifiable.
Pennsylvania state certification requires that voting systems be evaluated by a federally recognized independent testing authority, or voting system test laboratory (VSTL), and certified by the U.S. Election Assistance Commission (EAC) according to federal voting system standards.
Once you add that modem, you are de-certifying it, Kevin Skoglund, senior technical advisor at the National Election Defense Coalition said. It is no longer federally certified. And I dont know that all these jurisdictions are aware of that because ES&S is advertising otherwise. The three largest voting manufacturing companies Election Systems &Software, Dominion Voting Systems and Hart InterCivic have acknowledged they all put modems in some of their tabulators and scanners.-NBC
What youre going to find is the current Dominion and ES&S voting systems were designed over 22 years ago to allow and promote every type of voter fraud imaginable and the same two conspirators have been safeguarding and selling these broken systems the entire time.
From 1997 to 2003 Bob Urosevich and Barry Herron developed the art of electronic vote manipulation to such a degree; you didnt need to hack the system to change the election results. Below is the chain of custody for the software and source code that made this possible.
The key takeaway is simple. Although whats described below is from Diebold Election Systems, Dominion bought Diebold and this system for use. This the backbone of Dominion Voting Systems today and it gives a clear line of sight into the otherwise opaque world of election fraud in 2020.
In 2003, a research journalist named Bev Harris opened up the world of Diebold Election Systems. When Dominion Voting Systems got off the ground and became a player it was because of the purchase of Diebold properties including systems, source code, and software.
What she found was Diebold had a no-login needed website that was a detailed manual of how to hack the election systems Diebold was servicing across the US. If you didnt like the election tallies, it was a simple matter of replacing the file with one that reflected the results you wanted on this FTP site.
CDMedia is being de-platformed and obviously too effective! We need your support to put more reporters in the field! Help us here!
According to Harris, the site was set up for election workers and technicians and included hardware and software specifications, election results files, the vote-counting program itself, and replacement files for Diebolds GEMS vote-counting system and for the Windows software underlying the system.
The contents of these files amounted to a virtual handbook for vote-tampering: They contained diagrams of remote communications setups, passwords, encryption keys, source code, user manuals, testing protocols, and simulators, as well as files loaded with votes and voting machine software.
Diebold Elections Systems AccuVote systems use software called GEMS, and this system is used in 37 states. The voting system works like this:
Voters vote at the precinct, running their ballot through an optical scan, or entering their vote on a touch screen.
After the polls close, poll workers transmit the votes that have been accumulated to the county office. They do this by modem.
At the county office, there is a host computer with a program on it called GEMS. GEMS receives the incoming votes and stores them in a vote ledger. But in the files we examined, which were created by Diebold employees and/or county officials, we learned that the Diebold program used another set of books with a copy of what is in vote ledger 1. And at the same time, it made yet a third vote ledger with another copy.
Apparently, the Elections Supervisor never sees these three sets of books. All she sees is the reports she can run: Election summary (totals, county wide) or a detail report (totals for each precinct). She has no way of knowing that her GEMS program is using multiple sets of books, because the GEMS interface draws its data from an Access database, which is hidden. And here is what is quite odd: On the programs we tested, the Election summary (totals, county wide) come from the vote ledger 2 instead of vote ledger 1, and ledger 2 can be altered so it may or may not match ledger 1.
Now, think of it like this: You want the report to add up only the actual votes. But, unbeknownst to the election supervisor, votes can be added and subtracted from vote ledger 2. Official reports come from vote ledger 2, which has been disengaged from vote ledger 1. If one asks for a detailed report for some precincts, though, the report comes from vote ledger 1. Therefore, if you keep the correct votes in vote ledger 1, a spot check of detailed precincts (even if you compare voter-verified paper ballots) will always be correct.
Auditing
Again from Bev Harris provided all this information on a share-as-widely-as-possible basis. The audit trail is what is supposed to guarantee election security. Harris went to the same Diebold/Dominion website and downloaded a GEMS (General Election Management System) audit report.
Note that a user by the name of Evildoer was added. Evildoer performed various functions, including running reports to check his vote-rigging work, but only some of his activities showed up on the audit log.
It was a simple matter to eliminate Evildoer. First, we opened the election database in Access, where we opened the audit table: Then, we deleted all the references to Evildoer and, because we noticed that the audit log never noticed when the admin closed the GEMS program before, we tidily added an entry for that.
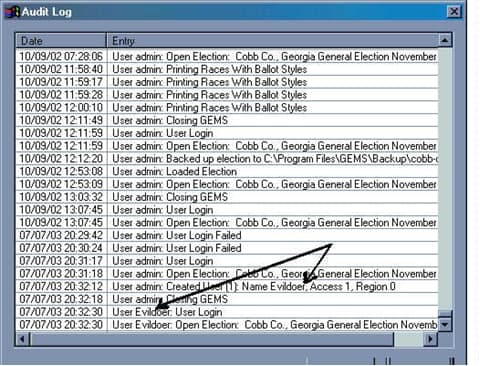
Access encourages those who create audit logs to use auto-numbering so that every logged entry has an uneditable log number. Then, if one deletes audit entries, a gap in the numbering sequence will appear. However, we found that this feature was disabled, allowing us to write in our own log numbers. We were able to add and delete from the audit without leaving a trace. Going back into GEMS, we ran another audit log to see if Evildoer had been purged:
As you can see, the audit log appears pristine.
In fact, when using Access to adjust the vote tallies we found that tampering never made it to the audit log at all. Bev Harris
An election (after the fact) using the real files on the real system was changed for research purposes with no elaborate hacking necessary.
The Dominion software and source code was originally developed by a company called Premier Election Solutions. The founder was Bob Urosevich.
In 1997 Global Election Systems acquired Premier. The company representatives were Bob Urosevich and Barry Herron
In 2001, Diebold purchased Global. The company representatives were Bob Urosevich and Barry Herron.
In 2009, Diebold Sells U.S. Elections Systems Business to ES&S. The company representatives were Bob Urosevich and Barry Herron
In September 2009, ES&S acquired Premier, without any objections from the DOJ. But in March 2010, the DOJ forced ES&S to sell Premiers assets to Dominion. ES&S was also forced to license to Dominion some of its software for free.
Dominion announced the acquisition of the Diebold (formerly Premier) products on May 19, 2010
Dominion Voting Systems purchased the primary assets of Premier, including all intellectual property, software, firmware, and hardware for Premiers current and legacy optical scan, central scan, and touch screen voting systems, and all versions of the GEMS election management system from ES&S.
Barry Herron is the Southeast regional sales manager for Dominion Voting Systems as well as being their lobbyist.
Barry Herron is Director of sales for INTERNATIONAL LOTTERY AND TOTALIZATOR, INC.
Barry Herron is the sales manager for Unisyn Voting. Unisyn, an HK registered company wholly owned by UNISYN VOTING SOLUTIONS (A DIVISION OF INTERNATIONAL LOTTERY AND TOTALIZATOR, INC) a division of Berjaya Lottery Management (h.k.) Ltd, a division of Yong Hong Group Co., Ltd., referred to Wing Hung Kai Group ( English: Wing Hung Kee Holdings Limiteds, HKEx except when licensing 0288.HK), founded in 1971, formerly known as Wing Hung Kai Properties Limited referred to as Wing-hong Kee Property ( English: Wing Hung Kee Investment Company, Limited ). Listed on the main board of the Hong Kong Stock Exchange in 1973. In 1994, the Malaysian consortium Berjaya Group ( Berjaya Group ) acquisition, changed its name to succeed Holdings (Hong Kong) Limited.
Unisyn is a wholly-owned private corporation headquartered in Malaysia but registered in Hong Kong, China.
INTERNATIONAL LOTTERY AND TOTALIZATOR, INC is the worlds largest manufacturer of voting machine equipment.
Does Unisyn manufacture Dominion Voting Solution machines? I dont have the answer to that but Unisyns Barry Herron is Dominions lobbyist for GA.
Along with Bob Urosevichs ES&S, Unisyn is also one of the voting systems companies certifying the 2020 US election was the safest in history.
How important is this information? If attorneys Rudy Guliani and Sydney Powell dont have this information yet, it will be vital in court to show the voting machine source code and system was known to be threats to national security in its previous use.
Throughout the rest of this article, Ill be referring to background The Case of the Diebold FTP Site Part of the Voting and Elections web pages by Douglas W. Jones Head of THE UNIVERSITY OF IOWA Department of Computer Science. The reference will be (DWJ). His study which refers to The Johns Hopkins Study On Voting Systems (Hopkins) as well as the SAIC (Science Applications International Corp). These three reports led to the decertification of the previous iteration of Dominions source code and software in various states and Dr. Jones has testified before Congress on these specific issues.
Ill also be referring to the NBC article (NBC), Online and vulnerable: Experts find nearly three dozen U.S. voting systems connected to internet which shows the problems the same voter software and source code used by Global Elections over 20 years ago is why Dominion Voting Systems/Diebold and ES&S/Diebold are still a national security threat today the same way they were labeled as such 17 years ago.
Lastly, How New Voting Machines Could Hack Our Democracy Jennifer Cohn for the New York Review of Books (NYRB) shows the updated methodology combined with Dominions source code makes election fraud easy. Comparing this to the Hopkins study or the paper by (DWG) its clear the level of threat election security is facing today.
At every waypoint in the election cycle from certification, planning, voting, absentee and mail-in votes, county reporting on the GEMS (General Election Management Systems), this system provides the means to monitor and change votes in real-time and even during the ballot reporting at the county level.
Throughout its history, whenever Diebold/Dominions source code, software, and method were inspected, it was moved under a new corporate logo.
How secure are the 2020 elections?
Cracking Dominions Source Code - A National Security Threat Since 2003
Using Modems for federal elections decertifies voting machines.
The state of Michigan is currently grappling with this issue. Since the 2016 election, Michigan authorized $82 million dollars to upgrade its election systems. Some of that money was spent on tabulators with wireless modems. But now, some state officials worry that the machines may pose a security risk and are pushing to have the modems removed.(NBC)
Some of the companies, agencies, groups, and people certifying the 2020 election as the safest in history represent a whos who of people to investigate for 2020 election fraud. If one voting system company is looked at under a microscope, more of them will fall soon thereafter.
For Georgia, this means the broken Diebold system Herron replaced with new Dominion machines is the same made to be hacked system Georgia already had with a few new add-ons.
LAN and hard lines
Because hacking into the systems is easy they way Diebold/Dominion set it up, according to (DWG)s report even the use of LAN and hard lines pose a significant security problem.
Allegation #53 (p. 16):
Physical access to the voting results may not even be necessary to acquire the voting records if they are transmitted across the Internet.
Diebold Response:
Results are not transmitted over the Internet.
My Added Comment:
But we know that result transmission uses telephone, PPP, and a username and password, from Page 14 of the Hopkins report, quoted in Allegation #40. Therefore, it is quite possible that election central will have a LAN connection using Internet protocol, perhaps used to connect a modem bank with a single PC. This LAN may not be as vulnerable as the public Internet, but it is vulnerable to packet snooping and several other attacks, and must therefore be carefully secured. Furthermore, if an adversary can dial into the PPP host and await connections, Trojan horse applications on the voting system could communicate with the adversary using PPP without talking to the GEMS system at all. (DWG)
In its previous iteration under the Diebold logo, access to GEMS was already provided. Using a latent Trojan or latent dynamic code that isnt detectable during certification or is added later and goes live during the election isnt just possible with this system. Every door for it happening has been left open for over 22 years of election cycles.
Diebold (now Dominion) made public assurances that GEMS servers were/are not connected to networks despite the fact that some were. If GEMS has a pool of modems it is connected to the telephone system and security depends on how the modems are managed and who is managing them. Telephone networks are considered part of the internet. A GEMS server could be dialed and corrupt data directly. The modem bank can be tunneled through to gain access to the polling places and corrupt election machines directly. (DWG)
That fact alone along with Dominion Voting Systems specifically being the owner of this system is enough to decertify not just the elections Dominion contracted for, but the equipment itself, already long considered a threat to election security.
Intrusion into the General Election Management System (GEMS)
From its inception this election system used 3rd party add-ons. This includes Microsoft Windows OS and Microsoft Office software which depending on the definition used for can be loaded with other COTS (commercial off the shelf 3rd party software).
The problem found with Microsoft components (DWG) is the use of dynamic coding which can be used to change ballot results. From the beginning (1997), Bob Urosevich and Barry Herron insisted this was not subject to a source code audit.
The same Microsoft ACCESS program is shown above to swiftly and undetectably change the audit trail and results is what Diebold/ES&S and Diebold/Dominion demand protection for.
When Diebold (using Dominions current source code) was audited by Metamor for the FEC/NASED, they found the security of GEMS and the integrity of the audit trails were compromised because Microsoft Access can easily change that audit trail.
Diebold (now Dominion) convinced Metamor this wasnt a problem for them because it was up to the customer to secure the election. In other words, they provided the means, training, and support for the crime, but cannot be held liable themselves.
According to (DWGs report) this was despite the fact that Diebold (now Dominion) was aware that this security was being routinely breached: Jane (I think it was Jane) did some fancy footwork on the .mdb file in Gaston [county Florida?] recently, I know our dealers do it. King County is famous for it. Thats why weve never put a password on the file before. [See BlackBoxVoting on Diebolds Internal Memos or Alteration of Audit Log Access.]
While this is damning, it only gets worse. After Diebolds source code was found on their website and examined, the code for the GEMS system used to manage elections and the Accutouch terminal was found. What became clear to (DWG) is the same code errors he pointed out half a decade earlier to Bob Urosevich and Barry Herron at Global Elections followed them to Diebold and was still in use.
This one point made Dr. Jones call for HYPERLINK http://avirubin.com/vote.pdf the decertification of the Diebold (Dominion) system directly after reading the John Hopkins University report.
Mail-in votes
In the (DWJ) report Diebolds (now Dominions) assertion that security loopholes in their voting system is of no importance because customer safeguards prevent exposure.
But, despite supervision in a San Louis Obispo County election, the GEMS system used to accumulate absentee and mail-in ballots were connected to the Diebold FTP site live and the tally of votes was noted midway through the election. For this to be posted on GEMS is normal for any election. How did Diebold comes into possession of this data and post it on their website?
Sneakernet
Before the internet existed, sneakernet was the way hacking was done by loading floppy discs or smartcards into the victims computer and adding malicious code or software.
Weve all seen the videos of thumb drives handed off during the 2020 election. The fact they werent secured should have decertified the results. Smartcards and thumb drives were noted in (DWG)s report as a major concern. In 2003, smartcards provided the interface for concern but these machines were not protected against inconspicuous devices like USB flash drives.
The locks on the machines themselves were noted to be so cheap it took no longer than 3 seconds to go past them. Gaining access took a team testing Diebold security 3 guesses to get the password and because Diebold (Dominion) uses the same login system-wide only one password gained supervisor credentials for every machine.
When Diebold/Dominions source code was read the researchers discovered a class of Security Key Cards that could be used to change default passwords.
Voting Machines
If it were the case that Diebolds machinery offered the possibility of a real audit of an election, in the same way that corporate accounting systems are supposed to be auditable, partisan bias on the part of the vendor would not be a problem, but this is not the case with direct-recording voting machines such as the Diebold AccuVote TS. Democrats want election machine firm thrown out, in the Port Clinton News Herald, August 27, 2003 and Voting machine controversy, in the Cleveland Plain Dealer, August 28.](DWG)
Universal Ballot Marking (BMDs)
According to Jennifer Cohns article on December 17, 2019 (NYRB), Universal use Ballot Marking Devices or BMDs function as electronic pens, mark your selections on paper on your behalf. Although vendors, election officials, and others often refer to this paper as a paper ballot, it differs from a traditional hand-marked paper ballot in that it is marked by a machine, which can be hacked without detection in a manual recount or audit. These pricey and unnecessary systems are sold by opaquely financed vendors who use donations and other gifts to entice election officials to buy them.
These scholars warn that even a robust manual audit, known as a Risk Limiting Audit, cannot detect whether a BMD-marked paper ballot has been hacked. BMDs instead put the burden on voters themselves to detect whether such ballots include fraudulent or erroneous machine marks or omissionseven though studies already show that many voters wont notice.
Andrew Appel, an election security expert at Princeton University, said Georgia currently has the least-secure voting machines now of any state and is right to replace them.
But he said the touchscreen ballot-marking devices and optical scanners of the new system are easily hackable. And the system relies on voters to check their own paper ballots when research shows they do a poor job of it.
Printed-out ballots will include the text of voters choices, but scanning machines will read computerized bar codes to count ballots.-AJC
This means the only real audit trail existing today is in the hands of voters when they leave the polling station. The BMD ballot they cast is unreadable barcode. Their ballot can be changed at every point along the way at the voting machine to the GEMS system.
Patches and new software
The ability to install patches or new software that wasnt certified has many risks, including the introduction of new bugs and more opportunities for tampering. It is even more risky if different patches can be installed at the last minute in particular jurisdictions, says David Dill, professor of computer science at Stanford University.
This opens the possibility of customized tampering by people who know exactly which races they want to affect, or bugs that are even less likely to be caught because they only occur in a small number of locations, says Dill. Of course, even if the certified code is frozen, it is easy to think of ways that undetectable back-doors could be installed in the software so that someone at the election site could choose the winner of the election. -Bev Harris
SAIC Conclusions on Dominions source code
The final paragraph of the executive summary of the SAIC report on the Diebold (now Dominion) system is pretty damning. The system is made to compromise. At the time six years had passed from the time the routes of compromise were discovered and Diebolds system, now owned by Dominion is the same.
The system, as implemented in policy, procedure, and technology, is at high risk of compromise. Application of the listed mitigations will reduce the risk to the system. Any computerized voting system implemented using the present set of policies and procedures would require these same mitigations. [Page V, final paragraph.]
See Risk Assessment Report: Diebold Accuvote-TS Voting System and Processes, SAIC-6099-2003-261, Sept 2, 2003]
Furthermore, since SAIC examined the current certified version of the code, the version number of which was redacted in the body of the text but exposed in Appendix D as 4.3.1.5, this seriously damages Diebolds claims that the flaws reported in the Hopkins study were in old code that is not used in real elections.- (DWG)
With an over 20 year history of providing every means of election fraud possible, training people how to do it, making sure elections are hackable, can Dominion or ES&S claim innocence in 2020?
These election vendors have a history thats mocked in Congress about the bribes they payout to the National Association of Secretaries of State (NASS) and other concerned parties.
Because the 2020 election season was Federal, every machine in every county that was hooked up to a modem was decertified for a federal election. In fact, the argument as shown above can be made for every system connected to any form of telephone systems as a backdoor to the internet and hackers.
Every state using the Dominion system ran decertified elections. The states elected to ignore federal election standards.
Can states that did not meet federal rules for elections after adding them into their own election certification requirements be considered legitimate participants in the 2020 election by choosing to ignore their own election standards?
The answer is no.
- Yssup Rider
- 12-29-2020, 05:33 PM
Neo should have taken the red pill.
I wonder if Trump will call him to testify when Dominion sues the shit out of him, Fox, Newsmax, OANN and the rest of the bullshit salesmen
I wonder if Trump will call him to testify when Dominion sues the shit out of him, Fox, Newsmax, OANN and the rest of the bullshit salesmen
- Redhot1960
- 12-29-2020, 07:28 PM
Don't use this Smilie ": rm_frog:" The 0zombie eccie Marxists will try to label you a Racist... "How You Say" Cancel Culture  1:02:00
1:02:00
https://www.nationalreview.com/2020/...-to-wokespeak/
A Guide to Wokespeak
Victor Davis Hanson
With the rise of the Left inevitable over the next two years, the public should become acquainted with the Left’s strange language of Wokespeak. Failure to do so could result in job termination and career cancellation. It is certainly a fluid tongue. Words often change their meanings as the political context demands. And what was yesterday’s orthodoxy is today’s heterodoxy and tomorrow’s heresy. So here is some of the vocabulary of the woke lexicon.
“Anti-racism.” Espousing this generic compounded -ism is far preferable to accusing particular people of being “racists” — and then being expected to produce evidence of their concrete actions and words to prove such indictments.
Instead, one can pose as fighting for “anti-racism” and thereby imply that all those whom one opposes, disagrees with, or finds distasteful, de facto, must be for “racism.”
“Anti-racism” is a useful salvo for students, teachers, administrators, public employees, political appointees, and media personnel to use peremptorily: declare from the start that you are working for “anti-racism” and then anyone who disagrees with you therefore must be racist, or, antithetically, “pro-racism.”
Oddly, such Wokespeak “anti-” adjectives denote opposition to something that no one claims to be for. For each proclaimed “anti-racist,” “anti-imperialist,” or “anti-colonialist,” there is almost no one who wishes to be a “racist” or desires to be a “colonialist” or an “imperialist.” These villains mostly come to life only through the use of their “anti-” adjectives.
“Disparate Impact.” This word is becoming anachronistic — call it Wokespoke, if you will. In ancient labor-law usage, it often accompanied the now equally calcified term “disproportional representation.” But in 21st-century American Wokespeak, it is no longer necessarily unfair, illegal, or unethical that some racial, gender, or ethnic groups are “over”-represented in certain coveted admissions and hiring.
Thus there can be no insidious, silent, or even inadvertent, but otherwise innate, bias that results in now-welcomed disproportional representation.
“Disparate” thus will likely be replaced by a more proper neologism such as “parity” or “affirmative” impact to denote that “overrepresentation” of one group over another is hardly “disparate,” but just and necessary to restore “parity” for past crimes of racism and sexism.
So disparate impact in general no longer has any systematic utility in matters of racial grievance and will soon be dropped. It was once a means to get to where we are and beyond. For example, at about 12 percent of the population, African Americans are disproportionally represented as players in both Major League Baseball (8 percent), and the National Basketball Association (75–80 percent), as are “whites” likewise in both sports, who constitute 65–70 percent of the general population, but make up only 45 percent of the MLB and 15–20 percent of the NBA. No constant term can be allowed to represent facts such as these.
“Cultural appropriation.” This adjective-noun phrase must include contextualization to be an effective tool in the anti-racism effort.
It does not mean, as the ignorant may infer from its dictionary entries, merely “the adoption of an element or elements of one culture or identity by members of another culture or identity.”
Asian Americans do not appropriate “white” or “European” culture by ballet dancing or playing the violin; “whites” or “Europeans” surely do appropriate Asian culture by using non-Asian actors in Japanese kabuki dance-drama.
For non–African Americans, dreadlocks or playing jazz are cultural appropriations; dying darker hair blond is not. A black opera soprano is hardly a cultural appropriationist. Wearing a poncho, if one is a non–Mexican-American citizen, is cultural theft; a Mexican-American citizen wearing a tuxedo is not.
Only a trained cultural appropriationist can determine such felonies through a variety of benchmarks. Usually the crime is defined as appropriation by a victimizing majority from a victimized minority. Acceptable appropriation is a victimized minority appropriating from a victimizing majority. A secondary exegesis would add that only the theft of the valuable culture of the minority is a felony, while the occasional use of the dross of the majority is not.
“Diversity.” This term does not include false-consciousness efforts to vary representation by class backgrounds, ideologies, age, or politics. In current Wokespeak, it instead refers mostly to race and sex (see “Race, class, and gender”), or in practical terms, a generic 30 percent of the population self-identified as non-white — or even 70 percent if inclusive of non-male non-whites.
“Diversity” has relegated “affirmative action” — the older white/black binary that called for reparatory “action” to redress centuries of slavery, Jim Crow, and institutionalized prejudice against African Americans — to the Wokespoke dustbin.
“Diversity” avoids the complications arising out of past actionable grievances, or worries about the overrepresentation or underrepresentation of particular tribes, or the class or wealth of the victimized non-white.
The recalibrated racially and ethnically victimized have grown from 12 percent to 30 percent of the population and need not worry whether they might lose advantageous classifications, should their income and net worth approximate or exceed that of the majority oppressive class.
“Diversity, equity, and inclusion.” This triad is almost always used in corporate, professional, and academic administrative titles, such as in a dean, director, or provost of “Diversity, Equity, and Inclusion.”
Known more commonly by their familiar, abbreviated sobriquets of “diversity czars,” such coveted billets are usually immune from budget cuts and economic belt-tightening. Often such newly created czar positions are subsidized in times of protest and financial duress by increasing the reliance on exploited part-time or low-paid workers, by either cutting or freezing their hours, benefits, or salaries.
No “equity czar,” for example, can afford publicly to be concerned about university exploitation of all part-time faculty. (See also under “Equity.”)
“Diversity” and “inclusion” are not synonymous or redundant nouns. Thus they should be used always in tandem: One can advocate for “inclusion” without oneself actually being “diverse,” or one can be “diverse” but not “include” others who are “diverse.” However, serving both diversity and inclusion ideally implies that those hired as non-white males are entrusted to hire additional non-white males.
“Equity.” Equity has now replaced the Civil Rights–era goal of “equality” — a word relegated to vestigial Wokespoke. After 60 years, equality apparently was exposed as a retrograde bourgeois synonym for the loaded “equality of opportunity” rather than a necessary, mandated “equality of result.”
Since seeking equality does not guarantee that everyone will end up the same, “equality” became increasingly unhelpful. Equity, in contrast, means that we do not just treat people at this late date “equally” — since most have been prior victims of various -isms and -ologies that require reparatory considerations.
“Equity” instead means treating people quite differently, even prejudicially so, to even the playing field for our past sins of economic, social, political, and cultural inequity.
“Hate speech.” Most of the incendiary “free speech” protected under the First Amendment is in actuality “hate speech,” and therefore deserves no such protection. If America were a properly woke society, then there would be no need for the First Amendment.
Like much of the vocabulary of Wokespeak, the notion of “hate speech” is not symmetrical. It cannot be diluted, subverted, and contextualized by false equivalencies. So the oppressed, occasionally in times of understandable duress, can use generic gender and race labels to strike back at the oppressor (see “Leveling the playing field”).
Crude stereotypes can be occasionally useful reminders for the victimized of how to balance the predictable hurtful vocabulary of the victimizer. In times of emotional trauma, the use by the oppressed of emphatics and colloquials such as “cracker,” “honky,” “gringo,” “whitey,” or “white trash” can serve as useful reminders of how “words matter.” In general, the rare and regrettable use of purported “hate speech” by one oppressed group against another is not necessarily hate speech, but usually a barometer of how a majority lexicon has marginalized the Other.
“Implicit bias.” “Implicit” is another handy intensifying adjective (see “Systemic racism”). Implicit bias, however, differs somewhat from “systemic racism.” It is analogous to a generic all-purpose antibiotic, useful against not just one pathogen but all pathogens, such as sexism, homophobia, nativism, transphobia, etc., that make up “bias,” a word that is now rarely used without an intensifying adjective.
Also, “implicit,” while implying “systemic,” additionally suggests chronological permanence, as in “innate bias.”
Thus “implicit bias” denotes a hard-to-detect prejudice against the non-heterosexual, the non-white, and the non-male that is sometimes as nontransparent as is it innate to the DNA of the heterosexual white male. Diversity trainers and workshops are needed to identify and inoculate against the virus of implicit bias.
“Intersectionality.” Race, class, gender, and other individual characteristics supposedly “intersect” with one another as shared victimizations. Thus, the community of the oppressed is commonly crisscrossed, and therefore amplified by such osmosis of shared grievances. The postmodern “intersectionality” has replaced the apparently now-banal term “rainbow coalition.”
In theory, the more shared victimizations, the higher the ranking one enjoys within the intersectional community.
However, when intersectionality results in stubborn tribal rivalries and struggles over identity-politics spoils, either one of two things follows: On the good side, those with the most oppressions (e.g., gay women of color) are the most rewarded accordingly. But on the bad side, the intersectional graph is blurred into rank Balkanization or worse.
A bellum omnium tribūum contra omnes tribūs follows, as the number of victims outnumbers the victimizers. Unfortunately, reparatory claims then must be fought over intrasectionally, i.e., each offended tribe unites monolithically in opposition to the others: e pluribus tribibus una becomes plures tribūs ex una.
“Leveling the playing field.” Sports terms can become useful Wokespeak. So to un-level the playing field is to “level” it. Leveling does not mean insisting on equality of opportunity (i.e., ensuring a soccer or rugby field does not slope in one direction), given inherent inequity. After all, when one team has not had access to proper training facilities, it deserves to play on an advantageously sloped field.
So to “level” means most certainly to slope the field for the benefit of one team, which in other matters allegedly suffers from past disadvantage brought on by bias that can only be corrected by and compensated through downhill advantage — or bias.
“LGBTQ.” This is currently the most widely used woke sobriquet for the homosexual and transgendered communities (see “Intersectionality”), although almost no one can agree on what the letter Q actually stands for.
Most clumsy politicians invoke the combined abbreviations — but often mangle and mix up the letters — without knowing really who does and does not qualify within the larger rubric. The term assumes there are few if any different agendas among homosexuals, lesbians, bisexuals, and the transgendered — at least that might outweigh their common nonbinary affinities.
“Marginalized.” The marginalized are those dehumanized by the white majority culture on the basis of race, sex, and sexual orientation. On rare occasions, the category can be difficult to articulate, given the intrusion of irrelevant class considerations that supposedly remedy “marginalization.” Income and wealth, however, are transitory criteria; sex and race are not. Jay-Z, Barack Obama, and LeBron James are permanently marginalized in a way that an unemployed Pennsylvania clinger is not.
“Micro-aggression.” “Micro” is another qualifying adjective of our subtler age in which active race- and gender-based prejudices are almost impossible for the novice to spot.
Instead, adept micro-aggression experts and skilled diversity trainers can detect double entendres, gestures, inexplicable silences, facial expressions, fashions, and habits — the “code” that gives one away as an offensive sexist or racist. Such skills, much like cryptography, as mastering a cult’s hand gestures can be taught through workshops to the general population to enable them to break these silent systems of insidious aggressions.
“Proportional representation.” This, and its negative twin, disproportional representation, is another ossified term (see “Disparate impact”) that has largely served its 1990s purpose and is now relegated to Wokespoke.
Originally, it meant that various minority groups deserved to be represented in hiring and admissions, and in popular culture, in numbers commensurate to their percentages in the general population.
But in 21st-century Wokespeak, the goal of ensuring “proportional representation” can now be racist, sexist, and worse — given that females enroll in, and graduate from, colleges in far greater numbers than their proportions of the general population, or that African Americans, from lucrative professional sports to coveted federal jobs such as the U.S. Postal Service, are represented in number greater than their percentages in the general population.
To reflect new demographics, proportionality is becoming questionable; disproportionality is now almost good.
“Race, class, and gender.” Another Wokespoke, Neanderthal tripartite term that is dropping out of Wokespeak.
“Class” no longer matters much in America. Billionaires Mark Zuckerberg and George Soros are not enemies of the people; white impoverished deplorables in West Virginia certainly are. Oprah is a victim. So are Facebook’s COO Sheryl Sandberg and Michelle Obama. Class is an anachronism.
To ensure distance from the irredeemables and clingers, Wokespeak will soon likely reduce the catechism to just “race and gender.”
“Safe space.” Safe spaces on college campuses (see “Theme house”) are not just segregated by race, gender, and sexual orientation; they are better described as official no-go zones for identifiable white heterosexual males. It would be debatable whether particular non-white or non-heterosexual or non-male groups can intrude into the segregated spaces of other particular groups. In general, these segregated enclaves offer sanctuary against “implicit bias” and “systemic racism.” Labeling them as “segregated spaces” is proof of implicit bias and systemic racism.
“Systemic racism.” “Systemic” belongs to this newer family of intensifying adjectival epithets (e.g., “micro,” “implicit,” etc.) that are necessary to posit a pathology that otherwise is hard to see, hear, or experience.
When one cannot point to actual evidence of “racism,” one can simply say that it is nowhere precisely because it is everywhere — sort of like the air we breathe that we count on, but often can’t see or feel.
“Theme house.” Theme houses are university dorms or sponsored off-campus student housing segregated by race. “Theme” is a useful euphemism for segregation, given that in theory there can be dorms for those of all races who share musical, artistic, or scholarly interests — or “themes,” e.g., an opera dorm or History House. But, in fact, “theme” today refers usually to race, gender, and ethnicity.
In Wokespeak, everyone is for theme houses; no one is for racially desegregating them. Being against the racial segregation of college dorms can become racist; being for them is never racist. Picking a future college roommate on the basis of race can be allowed — if neither the selector nor the selected is so-called “white.”
“The Other.” See under “Diversity.”
“Unearned white privilege”— as opposed to mere “white privilege.” The intensifier “unearned” is usually an added-on confessional by middle-aged white people in administrative or elite professional and coveted billets who wish to express their utmost penance for their high salaries, titles, and influence.
“Unearned,” however, is not to be confused with “undeserved.” Instead, it suggests certain white elites who wish to publicly confess their guilt for doing so well but without having to resign and to give back what they admittedly claim they did not earn.
Thus a college president is allowed to confess to having enjoyed “unearned” white privilege that nonetheless does not mean his present position is “undeserved.”
In sum, despite the fact that he was unfairly catapulted into the presidency, the college president’s manifest genius displayed after obtaining the job means he is now woke and clearly deserves to remain in the post. In other words, what explicit “unearned” was then, implicit “deserved” is now.
*****
 1:02:00
1:02:00https://www.nationalreview.com/2020/...-to-wokespeak/
A Guide to Wokespeak
Victor Davis Hanson
With the rise of the Left inevitable over the next two years, the public should become acquainted with the Left’s strange language of Wokespeak. Failure to do so could result in job termination and career cancellation. It is certainly a fluid tongue. Words often change their meanings as the political context demands. And what was yesterday’s orthodoxy is today’s heterodoxy and tomorrow’s heresy. So here is some of the vocabulary of the woke lexicon.
“Anti-racism.” Espousing this generic compounded -ism is far preferable to accusing particular people of being “racists” — and then being expected to produce evidence of their concrete actions and words to prove such indictments.
Instead, one can pose as fighting for “anti-racism” and thereby imply that all those whom one opposes, disagrees with, or finds distasteful, de facto, must be for “racism.”
“Anti-racism” is a useful salvo for students, teachers, administrators, public employees, political appointees, and media personnel to use peremptorily: declare from the start that you are working for “anti-racism” and then anyone who disagrees with you therefore must be racist, or, antithetically, “pro-racism.”
Oddly, such Wokespeak “anti-” adjectives denote opposition to something that no one claims to be for. For each proclaimed “anti-racist,” “anti-imperialist,” or “anti-colonialist,” there is almost no one who wishes to be a “racist” or desires to be a “colonialist” or an “imperialist.” These villains mostly come to life only through the use of their “anti-” adjectives.
“Disparate Impact.” This word is becoming anachronistic — call it Wokespoke, if you will. In ancient labor-law usage, it often accompanied the now equally calcified term “disproportional representation.” But in 21st-century American Wokespeak, it is no longer necessarily unfair, illegal, or unethical that some racial, gender, or ethnic groups are “over”-represented in certain coveted admissions and hiring.
Thus there can be no insidious, silent, or even inadvertent, but otherwise innate, bias that results in now-welcomed disproportional representation.
“Disparate” thus will likely be replaced by a more proper neologism such as “parity” or “affirmative” impact to denote that “overrepresentation” of one group over another is hardly “disparate,” but just and necessary to restore “parity” for past crimes of racism and sexism.
So disparate impact in general no longer has any systematic utility in matters of racial grievance and will soon be dropped. It was once a means to get to where we are and beyond. For example, at about 12 percent of the population, African Americans are disproportionally represented as players in both Major League Baseball (8 percent), and the National Basketball Association (75–80 percent), as are “whites” likewise in both sports, who constitute 65–70 percent of the general population, but make up only 45 percent of the MLB and 15–20 percent of the NBA. No constant term can be allowed to represent facts such as these.
“Cultural appropriation.” This adjective-noun phrase must include contextualization to be an effective tool in the anti-racism effort.
It does not mean, as the ignorant may infer from its dictionary entries, merely “the adoption of an element or elements of one culture or identity by members of another culture or identity.”
Asian Americans do not appropriate “white” or “European” culture by ballet dancing or playing the violin; “whites” or “Europeans” surely do appropriate Asian culture by using non-Asian actors in Japanese kabuki dance-drama.
For non–African Americans, dreadlocks or playing jazz are cultural appropriations; dying darker hair blond is not. A black opera soprano is hardly a cultural appropriationist. Wearing a poncho, if one is a non–Mexican-American citizen, is cultural theft; a Mexican-American citizen wearing a tuxedo is not.
Only a trained cultural appropriationist can determine such felonies through a variety of benchmarks. Usually the crime is defined as appropriation by a victimizing majority from a victimized minority. Acceptable appropriation is a victimized minority appropriating from a victimizing majority. A secondary exegesis would add that only the theft of the valuable culture of the minority is a felony, while the occasional use of the dross of the majority is not.
“Diversity.” This term does not include false-consciousness efforts to vary representation by class backgrounds, ideologies, age, or politics. In current Wokespeak, it instead refers mostly to race and sex (see “Race, class, and gender”), or in practical terms, a generic 30 percent of the population self-identified as non-white — or even 70 percent if inclusive of non-male non-whites.
“Diversity” has relegated “affirmative action” — the older white/black binary that called for reparatory “action” to redress centuries of slavery, Jim Crow, and institutionalized prejudice against African Americans — to the Wokespoke dustbin.
“Diversity” avoids the complications arising out of past actionable grievances, or worries about the overrepresentation or underrepresentation of particular tribes, or the class or wealth of the victimized non-white.
The recalibrated racially and ethnically victimized have grown from 12 percent to 30 percent of the population and need not worry whether they might lose advantageous classifications, should their income and net worth approximate or exceed that of the majority oppressive class.
“Diversity, equity, and inclusion.” This triad is almost always used in corporate, professional, and academic administrative titles, such as in a dean, director, or provost of “Diversity, Equity, and Inclusion.”
Known more commonly by their familiar, abbreviated sobriquets of “diversity czars,” such coveted billets are usually immune from budget cuts and economic belt-tightening. Often such newly created czar positions are subsidized in times of protest and financial duress by increasing the reliance on exploited part-time or low-paid workers, by either cutting or freezing their hours, benefits, or salaries.
No “equity czar,” for example, can afford publicly to be concerned about university exploitation of all part-time faculty. (See also under “Equity.”)
“Diversity” and “inclusion” are not synonymous or redundant nouns. Thus they should be used always in tandem: One can advocate for “inclusion” without oneself actually being “diverse,” or one can be “diverse” but not “include” others who are “diverse.” However, serving both diversity and inclusion ideally implies that those hired as non-white males are entrusted to hire additional non-white males.
“Equity.” Equity has now replaced the Civil Rights–era goal of “equality” — a word relegated to vestigial Wokespoke. After 60 years, equality apparently was exposed as a retrograde bourgeois synonym for the loaded “equality of opportunity” rather than a necessary, mandated “equality of result.”
Since seeking equality does not guarantee that everyone will end up the same, “equality” became increasingly unhelpful. Equity, in contrast, means that we do not just treat people at this late date “equally” — since most have been prior victims of various -isms and -ologies that require reparatory considerations.
“Equity” instead means treating people quite differently, even prejudicially so, to even the playing field for our past sins of economic, social, political, and cultural inequity.
“Hate speech.” Most of the incendiary “free speech” protected under the First Amendment is in actuality “hate speech,” and therefore deserves no such protection. If America were a properly woke society, then there would be no need for the First Amendment.
Like much of the vocabulary of Wokespeak, the notion of “hate speech” is not symmetrical. It cannot be diluted, subverted, and contextualized by false equivalencies. So the oppressed, occasionally in times of understandable duress, can use generic gender and race labels to strike back at the oppressor (see “Leveling the playing field”).
Crude stereotypes can be occasionally useful reminders for the victimized of how to balance the predictable hurtful vocabulary of the victimizer. In times of emotional trauma, the use by the oppressed of emphatics and colloquials such as “cracker,” “honky,” “gringo,” “whitey,” or “white trash” can serve as useful reminders of how “words matter.” In general, the rare and regrettable use of purported “hate speech” by one oppressed group against another is not necessarily hate speech, but usually a barometer of how a majority lexicon has marginalized the Other.
“Implicit bias.” “Implicit” is another handy intensifying adjective (see “Systemic racism”). Implicit bias, however, differs somewhat from “systemic racism.” It is analogous to a generic all-purpose antibiotic, useful against not just one pathogen but all pathogens, such as sexism, homophobia, nativism, transphobia, etc., that make up “bias,” a word that is now rarely used without an intensifying adjective.
Also, “implicit,” while implying “systemic,” additionally suggests chronological permanence, as in “innate bias.”
Thus “implicit bias” denotes a hard-to-detect prejudice against the non-heterosexual, the non-white, and the non-male that is sometimes as nontransparent as is it innate to the DNA of the heterosexual white male. Diversity trainers and workshops are needed to identify and inoculate against the virus of implicit bias.
“Intersectionality.” Race, class, gender, and other individual characteristics supposedly “intersect” with one another as shared victimizations. Thus, the community of the oppressed is commonly crisscrossed, and therefore amplified by such osmosis of shared grievances. The postmodern “intersectionality” has replaced the apparently now-banal term “rainbow coalition.”
In theory, the more shared victimizations, the higher the ranking one enjoys within the intersectional community.
However, when intersectionality results in stubborn tribal rivalries and struggles over identity-politics spoils, either one of two things follows: On the good side, those with the most oppressions (e.g., gay women of color) are the most rewarded accordingly. But on the bad side, the intersectional graph is blurred into rank Balkanization or worse.
A bellum omnium tribūum contra omnes tribūs follows, as the number of victims outnumbers the victimizers. Unfortunately, reparatory claims then must be fought over intrasectionally, i.e., each offended tribe unites monolithically in opposition to the others: e pluribus tribibus una becomes plures tribūs ex una.
“Leveling the playing field.” Sports terms can become useful Wokespeak. So to un-level the playing field is to “level” it. Leveling does not mean insisting on equality of opportunity (i.e., ensuring a soccer or rugby field does not slope in one direction), given inherent inequity. After all, when one team has not had access to proper training facilities, it deserves to play on an advantageously sloped field.
So to “level” means most certainly to slope the field for the benefit of one team, which in other matters allegedly suffers from past disadvantage brought on by bias that can only be corrected by and compensated through downhill advantage — or bias.
“LGBTQ.” This is currently the most widely used woke sobriquet for the homosexual and transgendered communities (see “Intersectionality”), although almost no one can agree on what the letter Q actually stands for.
Most clumsy politicians invoke the combined abbreviations — but often mangle and mix up the letters — without knowing really who does and does not qualify within the larger rubric. The term assumes there are few if any different agendas among homosexuals, lesbians, bisexuals, and the transgendered — at least that might outweigh their common nonbinary affinities.
“Marginalized.” The marginalized are those dehumanized by the white majority culture on the basis of race, sex, and sexual orientation. On rare occasions, the category can be difficult to articulate, given the intrusion of irrelevant class considerations that supposedly remedy “marginalization.” Income and wealth, however, are transitory criteria; sex and race are not. Jay-Z, Barack Obama, and LeBron James are permanently marginalized in a way that an unemployed Pennsylvania clinger is not.
“Micro-aggression.” “Micro” is another qualifying adjective of our subtler age in which active race- and gender-based prejudices are almost impossible for the novice to spot.
Instead, adept micro-aggression experts and skilled diversity trainers can detect double entendres, gestures, inexplicable silences, facial expressions, fashions, and habits — the “code” that gives one away as an offensive sexist or racist. Such skills, much like cryptography, as mastering a cult’s hand gestures can be taught through workshops to the general population to enable them to break these silent systems of insidious aggressions.
“Proportional representation.” This, and its negative twin, disproportional representation, is another ossified term (see “Disparate impact”) that has largely served its 1990s purpose and is now relegated to Wokespoke.
Originally, it meant that various minority groups deserved to be represented in hiring and admissions, and in popular culture, in numbers commensurate to their percentages in the general population.
But in 21st-century Wokespeak, the goal of ensuring “proportional representation” can now be racist, sexist, and worse — given that females enroll in, and graduate from, colleges in far greater numbers than their proportions of the general population, or that African Americans, from lucrative professional sports to coveted federal jobs such as the U.S. Postal Service, are represented in number greater than their percentages in the general population.
To reflect new demographics, proportionality is becoming questionable; disproportionality is now almost good.
“Race, class, and gender.” Another Wokespoke, Neanderthal tripartite term that is dropping out of Wokespeak.
“Class” no longer matters much in America. Billionaires Mark Zuckerberg and George Soros are not enemies of the people; white impoverished deplorables in West Virginia certainly are. Oprah is a victim. So are Facebook’s COO Sheryl Sandberg and Michelle Obama. Class is an anachronism.
To ensure distance from the irredeemables and clingers, Wokespeak will soon likely reduce the catechism to just “race and gender.”
“Safe space.” Safe spaces on college campuses (see “Theme house”) are not just segregated by race, gender, and sexual orientation; they are better described as official no-go zones for identifiable white heterosexual males. It would be debatable whether particular non-white or non-heterosexual or non-male groups can intrude into the segregated spaces of other particular groups. In general, these segregated enclaves offer sanctuary against “implicit bias” and “systemic racism.” Labeling them as “segregated spaces” is proof of implicit bias and systemic racism.
“Systemic racism.” “Systemic” belongs to this newer family of intensifying adjectival epithets (e.g., “micro,” “implicit,” etc.) that are necessary to posit a pathology that otherwise is hard to see, hear, or experience.
When one cannot point to actual evidence of “racism,” one can simply say that it is nowhere precisely because it is everywhere — sort of like the air we breathe that we count on, but often can’t see or feel.
“Theme house.” Theme houses are university dorms or sponsored off-campus student housing segregated by race. “Theme” is a useful euphemism for segregation, given that in theory there can be dorms for those of all races who share musical, artistic, or scholarly interests — or “themes,” e.g., an opera dorm or History House. But, in fact, “theme” today refers usually to race, gender, and ethnicity.
In Wokespeak, everyone is for theme houses; no one is for racially desegregating them. Being against the racial segregation of college dorms can become racist; being for them is never racist. Picking a future college roommate on the basis of race can be allowed — if neither the selector nor the selected is so-called “white.”
“The Other.” See under “Diversity.”
“Unearned white privilege”— as opposed to mere “white privilege.” The intensifier “unearned” is usually an added-on confessional by middle-aged white people in administrative or elite professional and coveted billets who wish to express their utmost penance for their high salaries, titles, and influence.
“Unearned,” however, is not to be confused with “undeserved.” Instead, it suggests certain white elites who wish to publicly confess their guilt for doing so well but without having to resign and to give back what they admittedly claim they did not earn.
Thus a college president is allowed to confess to having enjoyed “unearned” white privilege that nonetheless does not mean his present position is “undeserved.”
In sum, despite the fact that he was unfairly catapulted into the presidency, the college president’s manifest genius displayed after obtaining the job means he is now woke and clearly deserves to remain in the post. In other words, what explicit “unearned” was then, implicit “deserved” is now.
*****
